Nominations are closed. Voting is live until 15Mar.
It is time to reward members of the Unlock community who you think created the most value in the last month for the protocol and its community!
You have until March 8th to submit yourself or anyone’s address. After that, all token holders will have 7 days to vote (using Snapshot’s gas-less voting) on these addresses. When you submit someone, please include their Discord handle.
Anyone who receives more than 1% of the quadratic votes will be receiving their share of the 100 UDT allocated.
Please share their Discord handle and addresses and why you think they deserve to be retro-actively funded for their involvement during the month. Examples and pointers to participation are encouraged in the “why.” Examples and pointers help others in the community understand the context for the nomination.
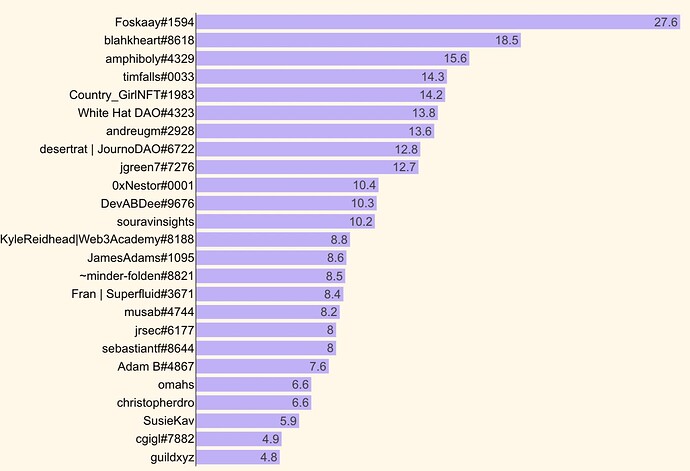
We also have the The Locksmith Leaderboard for February:
The Locksmith Leaderboard highlights active members of the Unlock Protocol community. Through participating via design, development, helping others in the community, sharing the Unlock Protocol story, and many other ways, Locksmiths are the core of Unlock Protocol and help propel the project forward.
The most visible places where Locksmiths engage with the project and each other are on Github (adding issues, submitting pull requests, creating projects that integrate Unlock), on Twitter (sharing and mentioning Unlock Protocol in their social media activities), and in the project Discord (responding to and answering question threads). The Leaderboard also attempts to capture longevity of participation in the community, as well as consistency of participation over time.
You can read more on The Locksmith Leaderboard page on Notion.
https://unlockprotocol.notion.site/Locksmith-Leaderboard-c620b5b00e2d404d9f1a20f2e11130d8
We hope the Locksmith Leaderboard can give you some visibility into the breadth and depth of individuals who are active in the Unlock Protocol community and provide some context as you are making your nominations for retroactive funding. Like everything, the Leaderboard and the retroactive funding process will evolve over time.
Looking forward to seeing your nominations!